As the pandemic continues to keep many workers home from the office, companies are using cloud services and apps more than ever. This heightened use of virtual tools has led to an increase in certain types of phishing attacks. In particular, we are seeing a rise in consent phishing.
What is it?
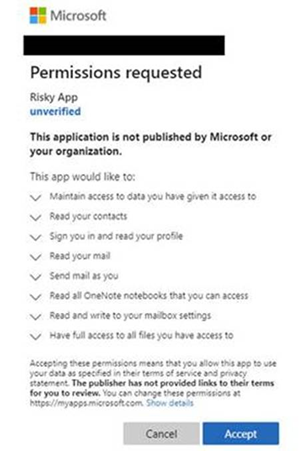
Consent phishing is a specialized type of phishing. It gives an attacker access to private information by tricking users into providing permissions through the installation of a malicious app. Using OAuth 2.0 technology, a developer can allow a user to grant access to certain data without having to use credentials. Firstly, an attacker creates an app, often spoofing or making references to trusted sources. Then they send the link via traditional phishing emails or place it on a compromised website. If the user downloads the app and accepts the permissions, the attacker will have access to private data through the app. The app receives an access token which can be used to make Application Program Interface (API) calls. This allows the attacker to access sensitive data such as files, email, and contacts.
“Part of the problem is that most users don’t understand what is happening. They don’t know that a sign-on that they’ve used with Gmail, Facebook, Twitter or some other OAuth provider is now automatically being called and used or abused by another person. They don’t understand the permission prompts either. All they know is they clicked on an email link or an attachment and now their computer system is asking them to confirm some action that they really don’t understand.”
– Roger Grimes, KnowBe4
In the News
The SANS Institute is the largest cybersecurity training and certification company in the world. They were recently victims of a data breach as a result of a consent phishing attack.
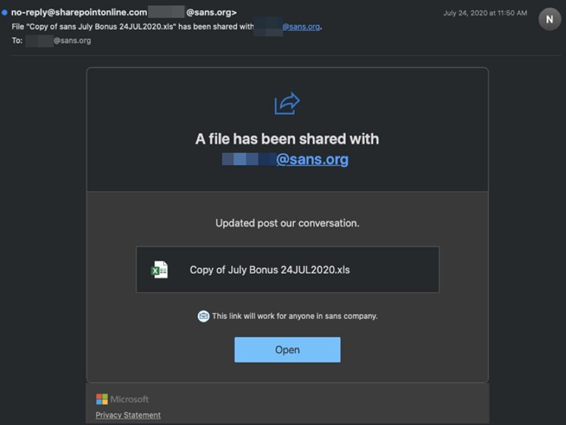
It began when several employees received a phishing email. The email contained a link to what purported to be bonus information. The link looked like a Microsoft SharePoint file share. According to Jim Yacone of SANS, “One employee clicked the link and authorized installation of the malicious add-in, which allowed for the creation of the forwarding rule.” The forwarding rule sent 513 emails to the attacker. Consequently, just one person’s email account exposed approximately 28,000 records with Personally Identifiable Information (PII).
The SANS Institute is a highly regarded company for educating users on cybersecurity. Even so, they still had an employee fall for a phishing scam. If even people working in cybersecurity are falling for consent phishing, how can we protect ourselves and our businesses?
Prevention
As with most internet scams, education is important. Here are a few tips to avoid falling for a consent phishing scam.
- Pay attention. As with regular phishing emails, watch for poor spelling and grammar. Hover over links before clicking. Type the link into a browser instead of clicking. Check the sender.
- Review all permissions prompts before agreeing when downloading a new app.
- Look out for spoofed app names and URLs. Only approve permission requests from app names you know and trust.
- Use apps with verified publishers.
- Use multi-factor authentication.
- Put application consent policies in place. Companies should also audit apps and consent permissions regularly.
IPS has been working in anti-phishing and fraud protection for nearly two decades. During this time, we have seen how quickly and constantly fraud tactics evolve. It’s important to be aware of new trends in cybersecurity to better protect your information. Let us know if we can help your company.

written by
Theresa Farrell
September 15, 2020
Stay informed with industry-relevant emails curated by our team of experts.
We send out emails once or twice a month relating to IP Services, industry news, and events we'll be attending so you can meet our experts in person.

Theresa Farrell
Theresa joined IP Services over a decade ago after graduating with a bachelor’s degree in Finance. She previously worked on both the Fraud Prevention and Privacy & Compliance teams. For most of her tenure, she has worked in Program Management as a Program Support Specialist which includes event planning, metrics reporting, program development and communication management.